Considering 4K CCTV? Our findings will surprise you …
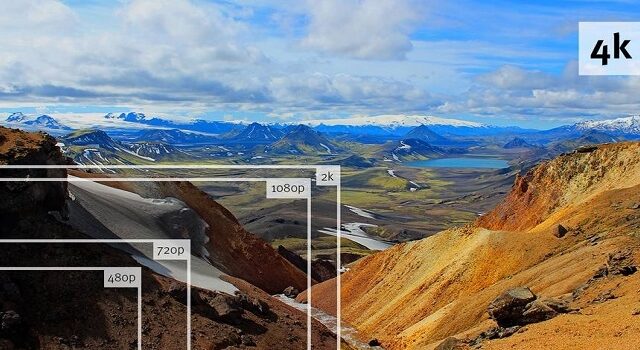
Twelve months ago, I wrote an article on CCTV called “Don’t Buy The Hype”. The article talked about some of the often and outrageous claims by CCTV vendors and the emergence of 4K cameras.
In this article, we assess 3 different camera manufacturers, show you some real-world results and highlight the differences in camera performance.
We also outline the 3 most important questions you need to ask before even considering 4K CCTV, particularly for external applications.
The findings will interest you.
Read More »The two biggest security threats of 2016

In 2016, companies on a global scale will be more exposed to security risks than ever before.
While 2015 was a high-risk year, we somehow managed to get through it unscathed, either by good management or simply good luck.
However, in 2016 businesses of all sizes will face two single security threats that have the potential to financially cripple businesses if the proper risk management strategies are not in place.
Read More »Overseas hackers blamed for school bomb scare

Police believe that the series of bomb threats received at several Australian schools since Friday is the work of overseas hackers. Dozens of schools in NSW, Canberra, Victoria and Queensland have received the same automated phone message warning of a device on school grounds. Security expert Luke Percy-Dove, said from what has been reported, the
Read More »How is your duress system performing? Take this quick test

Duress systems have featured heavily in each of the risk assessments we have completed recently. The most common factor with all of them has been how poorly they have been considered being implemented. And this is a real concern.
We have developed a quick checklist to help identify what you need to do for your system to perform better.
Read More »Latest App allows Security Guards to be more mobile

Security guards are an expensive resource.
Here in Australia, it costs well over $300,000 a year to have a 24/7 security presence and much more for larger sites where multiple guards may be required.
The latest App by Gallagher which is specifically designed for the Apple iPhone, immediately allows security guards to be more mobile and spend more time on patrol performing security functions.
Read More »CCTV Monitoring – The elephant in the room

Watching CCTV may sound like good fun for some, but soon enough it becomes quite mundane.
The challenge with actively monitored CCTV systems is ensuring that operators remain focused at all times.
Research indicates that after 12 minutes of continuous video monitoring an operator will often miss up to 45% of screen activity.
Read More »Mobile duress devices – Safety watch
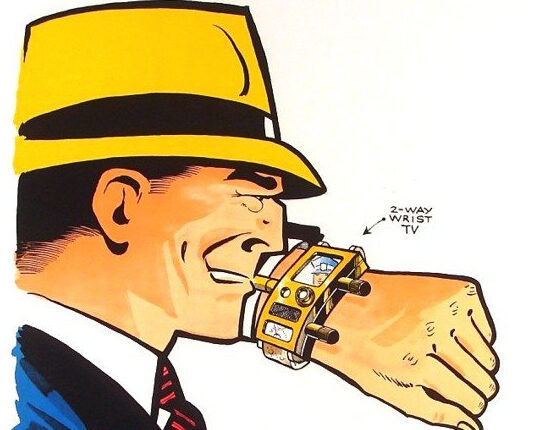
The next generation of these devices are now coming to market with a much higher level of intelligence.
What the manufacturers are doing now is adopting the principle first explored by Dick Tracy in 1946 and more recently by Apple, by making 2-way communications wearable in the form of a duress smart watch.
Read More »The convergence of security disciplines

The term “convergence” has become a bit of a buzz word in security as a result of physical security technologies becoming more akin to information security technologies and the cross over between the two disciplines.
This was always going to happen and as a result, we are seeing a noticeable shift in the global physical security market.
Read More »Innovative use of CCTV – Latest Porsche billboard

In May this year, we provided an example of how CCTV in conjunction with facial recognition technology was being used to heighten awareness of domestic violence.
To demonstrate the versatility that CCTV can bring to business, here is another example of billboard advertising by luxury sports car manufacturer, Porsche.
Read More »Security Risk Assessment – 5 Signs that you may need a second opinion

The accepted best practice for identifying risk is through the undertaking of a security risk assessment.
The risk assessment process is tightly structured to ensure that all visible risk is identified. Once completed, the risk assessment will shine a light on where risks exist, allowing you to put a strategy in place to mitigate those risks.
Read More »